[sc name=”ad_1″] HyperDbg is designed with a focus on using modern hardware technologies to provide new features to the reverse engineering world...
Search Results For - Diagram
[sc name=”ad_1″] We at OpenEDR believe in creating a cybersecurity platform with its source code openly available to public, where products and...
[sc name=”ad_1″] Process Herpaderping is a method of obscuring the intentions of a process by modifying the content on disk after the image has...
[sc name=”ad_1″] Threagile (see for more details) is an open-source toolkit for agile threat modeling: It allows to model an architecture with its...
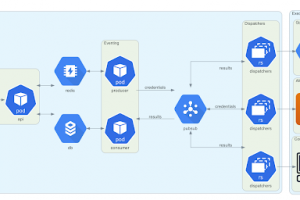
[sc name=”ad_1″] The Trident project is an automated password spraying tool developed to meet the following requirements: the ability to be...
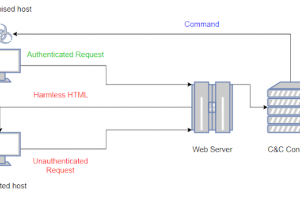
[sc name=”ad_1″] LOLBITS is a C2 framework that uses Microsoft’s Background Intelligent Transfer Service (BITS) to establish the...
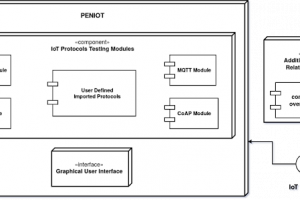
[sc name=”ad_1″] PENIOT is a penetration testing tool for Internet of Things (IoT) devices. It helps you to test/penetrate your devices by...
[sc name=”ad_1″] Threat Dragon is a free, open-source, cross-platform threat modeling application including system diagramming and a rule engine to...
[sc name=”ad_1″] SGN is a polymorphic binary encoder for offensive security purposes such as generating statically undetecable binary payloads. It...
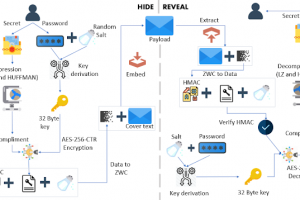
[sc name=”ad_1″] StegCloak is a pure JavaScript steganography module designed in functional programming style, to hide secrets inside text by...